Information Security
Basic Approach
Guided by our mission to "paint an innovative future with cutting-edge microfabrication technology" through photomask manufacturing, we prioritize customer trust above all else. We recognize the appropriate and secure management of information and systems as a critical management objective.
As we strive to become a globally preferred enterprise following our IPO, strengthening information security management and cybersecurity processes is indispensable. We consider this to be one of the foundations supporting the provision of safe and secure products and services.
Our business relies on highly confidential information including both customer and company intellectual property. Properly protecting this information is essential to meet the customer requirements in the markets we serve.
In recent years, the sophistication of IoT and the advancement of digitalization have increased the threat of cyberattacks, heightening the risk not only of information leaks but also of threats to business continuity itself.
To address these risks, we have established our "Information Security Policy" and "Privacy Policy," promoting integrated countermeasures from technical, organizational, physical, and human perspectives.
Specifically, we are strengthening access controls, implementing a zero-trust model, and enhancing monitoring and incident response systems.
Furthermore, we provide ongoing training to ensure all employees recognize information security as their own responsibility and can perform their duties under globally unified policies.
To address the increasing security risks across the entire supply chain, we are working to reduce risks through security assessments of contractors handling important information.
Based on our MVV, we are committed to strengthening the foundation of trust that supports our corporate activities by working as One Team to manage information security thereby strengthening the foundation of trust that underpins our corporate activities.
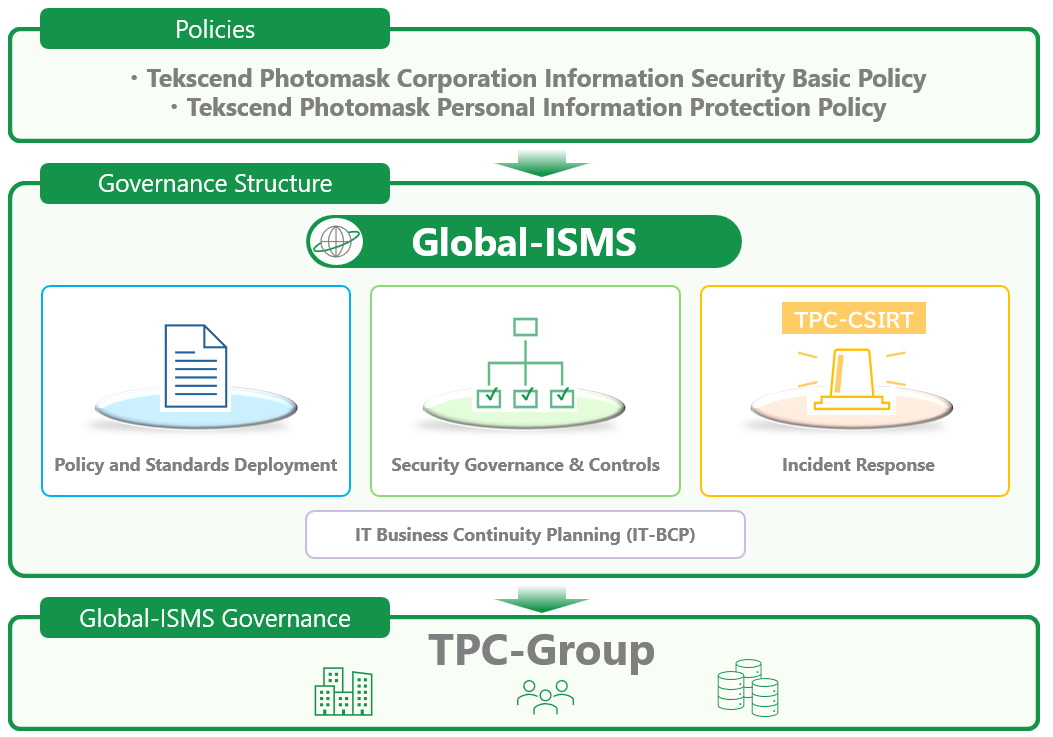
Information Security Management and Framework (Organizational Security Measures)
Based on globally unified policies, we have established the TPC Global-ISMS (Tekscend Photomask Corp Global Information Security Management System) to centrally manage information security administration and operations.
Information Security Governance Management Framework
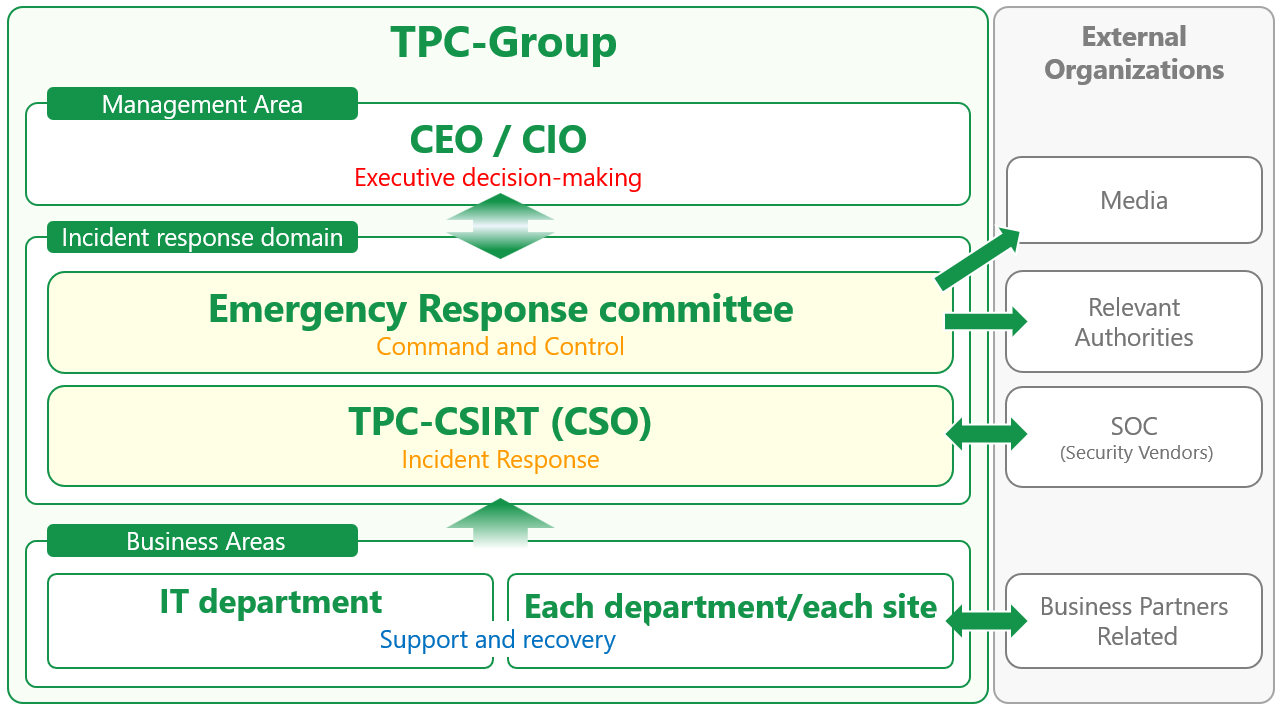
Incident Response Management System
Implementation of Various Security Measures
Facility Management (Physical Security Measures)
Our facilities are equipped with diverse physical security measures, such as flap gates, surveillance cameras, and magnetic sensors, tailored to the defined security levels for each region, site, and area, restricting access to non-authorized personnel.
Countermeasures Against Cyber Attacks (Technical Security Measures)
1. Corporate Security
As cyberattacks targeting enterprises, such as ransomware, become increasingly sophisticated, we manage security globally as One Team, fundamentally based on the ※ ZTNA (Zero Trust Network Access) model.
※ A security model that does not rely on traditional perimeter defenses
(1) Establishment and Operation of CSIRT
Starting in fiscal year 2024, we organized the TPC-CSIRT (Computer Security Incident Response Team), which leads threat analysis and response based on incident alerts from the SOC (Security Operation Center) and external threat intelligence.
(2) Establishment and Operation of the SOC
The SOC continuously monitors our IT systems, rapidly detects external intrusions and internal misconduct, and collaborates with TPC-CSIRT to support activities aimed at preventing incidents and achieving early resolution.
2. Factory Security
We consider the factory network (Operational Technology), which handles customer data and our critical technical information, to be the most important area. It is separated from other internal networks and managed with strict controls. Based on internal regulations, we conduct regular vulnerability assessments and strive to minimize vulnerabilities.
3. AI Security
We place significant importance on the immense potential for creating new value through the effective use of AI (Artificial Intelligence). To prepare for its risks and ensure fair judgment, we have established and operate AI guidelines based on ISO 42001 for our development processes when utilizing AI.
Information Security Training (Human Resource Security Measures)
We conduct information security training for all employees to ensure thorough understanding of rules and educate on the latest critical matters.
| No. | Training Name | Frequency | Overview |
|---|---|---|---|
| 1 | New Employee Training | Once a year | Common training for regular hires |
| 2 | Mid-Career Hire Training | As needed | Basic Training for Mid-Career Hires |
| 3 | Annual Training | Once a year | Common training incorporating timely updates to basic education |
| 4 | Role-Based Training | As needed | Education tailored to responsibilities and roles |
| 5 | Training for email attacks | Multiple times per year | Resilience-building training using simulated email attacks |
Protection of Personal and Privacy Information
We comply with and appropriately address laws and regulations established in each country and region.
Continuous Improvement
To address the ever evolving and increasingly sophisticated information security risks and to continue providing our customers with advanced products, we must constantly adapt our security processes.
We refer to the following framework to plan and execute various countermeasures.
Additionally, we compile a cybersecurity report every six months to visualize the status of countermeasure implementation.
ISO 27001 (Certified)
ISO 15408 (Certified)
CMMC (Certification Planned)
ISO 62443
ISO 42001
NIST 800-61
NIST 800-171
NIST Cybersecurity Framework
Cybersecurity Management Guidelines
Third-Party Assessment and Certification Status
Supply Chain Risk Management
We recognize the increasing information security risks through the supply chain and are advancing initiatives to reduce risks that could impact on our business activities.
Specifically, at the start of business relationships, we conduct risk assessments considering the nature of our partners' businesses and the importance of the information they handle. We also enter into non-disclosure agreements (NDAs) to ensure the appropriate handling of confidential information.
We will continue to strive for the protection of information assets and stable business operations by building appropriate relationships with each company within the supply chain.
Conclusion
With the advancement of digital technology, the risks surrounding information security and cybersecurity are constantly evolving. In this environment, we believe that to protect the value of the products and services we have built and to continue to meet society's trust, it is essential to go beyond technical measures and implement continuous, comprehensive efforts encompassing our organization, people, and processes.
Based on our MVV, we will continuously review and improve our approach to information security, with all our global locations collaborating as One Team.
By flexibly responding to evolving threats, business environments, and societal demands, we will strengthen information security not merely as a defensive measure, but as a critical management foundation supporting enhanced corporate value and sustainable growth.
Moving forward, we will deepen trust with our customers and society by providing safe and secure products and services, contributing to the realization of a sustainable society.